Exploring the intersection of natural sciences and information technology via entropy and randomness
Bennett, D. J. Randomness (Harvard University Press, 1998).
Moyer, A. E. Liber de ludo aleae. Renaiss. Q. 60, 1419–1420 (2007).
Sheynin, O. B. Early history of the theory of probability. Arch. Hist. Exact. Sci. 17, 201–259 (1977).
Google Scholar
Herrero-Collantes, M. & Garcia-Escartin, J. C. Quantum random number generators. Rev. Mod. Phys. 89, 015004 (2017).
Google Scholar
Shannon, C. E. A mathematical theory of communication. Bell Labs Tech. J. 27, 379–423 (1948).
Google Scholar
Dittrich, T. ‘The concept of information in physics’: an interdisciplinary topical lecture. Eur. J. Phys. 36, 015010 (2014).
Kuhn, T. S. The Structure of Scientific Revolutions (University of Chicago Press, 1963).
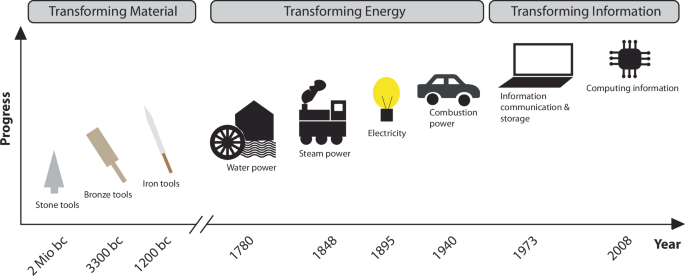
Hilbert, M. Digital technology and social change: the digital transformation of society from a historical perspective. Dialogues Clin. Neurosci. 22, 189–194 (2020).
Castells, M. The iNformation Age: Economy, Society and Culture (Blackwell, 2020).
Grobe, K., Eiselt, M. Wavelength Division Multiplexing: A Practical Engineering Guide (John Wiley & Sons, 2013).
Hilbert, M. & López, P. The world’s technological capacity to store, communicate, and compute information. Science 332, 60–65 (2011).
Google Scholar
Shannon, C. E. The bandwagon. IRE Trans. Inf. Theory 2, 3 (1956).
Lineweaver, C. H. The entropy of the universe and the maximum entropy production principle. In Beyond the Second Law: Entropy Production and Non-Equilibrium Systems (eds Dewar R. C., Lineweaver C. H., Niven R. K. & Regenauer-Lieb, K.) (Springer, 2014).
Kaila, V. R. I. & Annila, A. Natural selection for least action. Proc. R. Soc. A 464, 3055–3070 (2008).
Google Scholar
Kostic, M. M. The elusive nature of entropy and its physical meaning. Entropy 16, 953–967 (2014).
Google Scholar
Basurto-Flores, R., Guzmán-Vargas, L., Velasco, S., Medina, A. & Calvo Hernández, A. On entropy research analysis: cross-disciplinary knowledge transfer. Scientometrics 117, 123–139 (2018).
Google Scholar
Ribeiro, M. et al. The Entropy Universe. Entropy 23, 222 (2021).
Google Scholar
Clausius, R. Abhandlungen über die mechanische Wärmetheorie (F. Vieweg und Sohn, 1864).
Gibbs, J. W. On the equilibrium of heterogeneous substances. Am. J. Sci. 3, 441–458 (1878).
Google Scholar
Lucia, U. Mathematical consequences of Gyarmati’s principle in rational thermodynamics. Il Nuovo Cim. B 110, 1227–1235 (1995).
Google Scholar
Layzer, D. The arrow of time. Sci. Am. 233, 56–69 (1975).
Nelson, P. G. Understanding entropy. Found. Chem. 24, 3–13 (2022).
Alzeer, J. Directionality of chemical reaction and spontaneity of biological process in the context of entropy. Int. J. Regenr. Med. 5, (2022).
Crooks, G. E. Entropy production fluctuation theorem and the nonequilibrium work relation for free energy differences. Phys. Rev. E 60, 2721 (1999).
Google Scholar
Jarzynski, C. Nonequilibrium equality for free energy differences. Phys. Rev. Lett. 78, 2690–2693 (1997).
Google Scholar
Sandler, S. I. An Introduction to Applied Statistical Thermodynamics (John Wiley & Sons, 2010).
Dugdale, J. S. Entropy and its Physical Meaning (Taylor & Francis, 2018).
Boltzmann, L. The second law of thermodynamics. In Theoretical Physics and Philosophical Problems: Selected Writings (Springer, 1974).
Bennett, C. H. The thermodynamics of computation—a review. Int. J. Theor. Phys. 21, 905–940 (1982).
Landauer, R. Irreversibility and heat generation in the computing process. IBM J. Res. Dev. 5, 183–191 (1961).
Google Scholar
Maxwell’s Demon: Entropy, Information, Computing (eds Leiff H. S. & Rex, A. F.) (Taylor & Francis, 1990).
Maruyama, K., Nori, F. & Vedral, V. Colloquium: the physics of Maxwell’s demon and information. Rev. Mod. Phys. 81, 1–23 (2009).
Google Scholar
Parrondo, J. M. R., Horowitz, J. M. & Sagawa, T. Thermodynamics of information. Nat. Phys. 11, 131–139 (2015).
Google Scholar
Jaynes, E. T. Information theory and statistical mechanics. Phys. Rev. 106, 620 (1957).
Google Scholar
Layzer, D. The arrow of time. Astrophys. J. 206, 559–569 (1976).
Google Scholar
Rajasekaran, S., Reif, J. H. Derivation of randomized sorting and selection algorithms. In Parallel Algorithm Derivation and Program Transformation. The Springer International Series In Engineering and Computer Science (eds Paige R., Reif J. & Watcher, R.) (Springer, 1993).
Rabin, M. O. Probabilistic algorithm for testing primality. J. Number Theory 12, 128–138 (1980).
Google Scholar
Kroese, D. P. & Rubinstein, R. Y. Monte Carlo methods. Wiley Interdiscip. Rev. Comput. Stat. 4, 48–58 (2012).
Schmidt, J. F., Schilcher, U., Vogell, A. & Bettstetter, C. Using randomization in self-organized synchronization for wireless networks. ACM Trans. Auton. Adapt. Syst. 9, 1–20 (2023).
Gennaro, R. Randomness in cryptography. IEEE Secur. Priv. 4, 64–67 (2006).
Samid, G. Pattern devoid cryptography. Cryptology ePrint Archive, (2021).
Hiltgen, A., Kramp, T. & Weigold T. Secure Internet banking authentication. IEEE Secur. Priv. 4, 21–29, (2006).
Stipčević, M. & Koç, Ç. K. True random number generators. In Open Problems in Mathematics and Computational Science (Springer, 2014).
Sunar, B. True Random Number Generators for Cryptography. In Cryptographic Engineering (ed. Koç, ÇK) (Springer, 2009).
Petitcolas, F. A. P. Kerckhoffs’ Principle. In Encyclopedia of Cryptography and Security (eds van Tilborg H. C. A. & Jajodia, S.) (Springer, 2011).
Shannon, C.E. Communication theory of secrecy systems. In Proc. The Bell System Technical Journal (IEEE, 1949).
Gong, L., Zhang, J., Liu, H., Sang, L. & Wang, Y. True random number generators using electrical noise. IEEE Access 7, 125796–125805 (2019).
Guo, H., Tang, W., Liu, Y. & Wei, W. Truly random number generation based on measurement of phase noise of a laser. Phys. Rev. E 81, 051137 (2010).
Google Scholar
Li, X., Cohen, A. B., Murphy, T. E. & Roy, R. Scalable parallel physical random number generator based on a superluminescent LED. Opt. Lett. 36, 1020–1022 (2011).
Google Scholar
Pimbblet, K. A. & Bulmer, M. Random numbers from astronomical imaging. Publ. Astron. Soc. Aust. 22, 1–5 (2005).
Google Scholar
Ruschen, D., Schrey, M., Freese, J., Heisterklaus, I. Generation of true random numbers based on radioactive decay. In Proc. 21st International Student Conference on Electrical Engineering (Springer, 2017).
Gavrylko, R. & Gorbenko, Y. І A physical quantum random number generator based on splitting a beam of photons. Telecommun. Radio Eng. 75, 179–188 (2016).
Garfinkel, S. L., Leclerc, P. Randomness Concerns when Deploying Differential Privacy. In: WPES’20: Proceedings of the 19th Workshop on Privacy in the Electronic Society (Association for Computing Machinery, 2020).
Szczepanski, J., Wajnryb, E., Amigó, J. M., Sanchez-Vives, M. V. & Slater, M. Biometric random number generators. Comput. Secur. 23, 77–84 (2004).
Erbay, C., Ergün, S. Random Number Generator Based on Micro-Scale Bio-electrochemical Cell System. In: 2019 17th IEEE International New Circuits and Systems Conference (NEWCAS) (IEEE, 2019).
Yoon, I., Han, J. H., Park, B. U. & Jeon, H.-J. Blood-inspired random bit generation using microfluidics system. Sci. Rep. 14, 7474 (2024).
Google Scholar
Diffie, W. & Hellman, M. E. New directions in cryptography. In Proc. IEEE Transactions on Information Theory (IEEE, 1976).
Pappu, R., Recht, B., Taylor, J. & Gershenfeld, N. Physical one-way functions. Science 297, 2026–2030 (2002).
Google Scholar
Shor, P. W. Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer. SIAM Rev. 41, 303–332 (1999).
Google Scholar
Rührmair, U., Sölter, J. & Sehnke, F. On the foundations of physical unclonable functions. Cryptology ePrint Archive, Report No. 2009/2277 (The International Association for Cryptologic Research, 2009).
McGrath, T., Bagci, I. E., Wang, Z. M., Roedig, U. & Young, R. J. A PUF Taxonomy. Appl. Phys. Rev. 6, 11303 (2019).
Herder, C., Yu, M. D., Koushanfar, F. & Devadas, S. Physical unclonable functions and applications: a tutorial. In Proc. IEEE (IEEE,2014).
Gao, Y. S., Al-Sarawi, S. F. & Abbott, D. Physical unclonable functions. Nat. Electron. 3, 81–91 (2020).
Yu, M. D. & Devadas, S. Secure and robust error correction for physical unclonable functions. IEEE Des. Test. Comput. 27, 48–64 (2010).
Google Scholar
Delvaux, J., Gu, D., Schellekens, D. & Verbauwhede, I. Helper data algorithms for PUF-based key generation: overview and analysis. IEEE Trans. Comput. Aided Des. 34, 889–902 (2015).
Bösch, C., Guajardo, J., Sadeghi, A. R., Shokrollahi, J. & Tuyls, P. Efficient helper data key extractor on FPGAs. In Proc. Cryptographic Hardware and Embedded Systems – CHES 2008) (Springer, 2008).
Guajardo, J., Kumar, S. S., Schrijen, G. J. & Tuyls, P. FPGA intrinsic PUFs and their use for IP protection. In Proc. Cryptographic Hardware and Embedded Systems – Ches 2007 (Springer, 2007).
Gassend, B., Clarke, D., van Dijk, M. & Devadas, S. Silicon physical random functions. In Proc. 9th ACM Conference on Computer and Communications Security (ACM, 2002).
Holcomb, D. E., Burleson, W. P. & Fu, K. Power-up SRAM state as an identifying fingerprint and source of true random numbers. IEEE Trans. Comput. 58, 1198–1210 (2009).
Google Scholar
Ahn, J. et al. Nanoseed-based physically unclonable function for on-demand encryption. Sci. Adv. 11, eadt7527 (2025).
Google Scholar
Kim, J. H. et al. Nanoscale physical unclonable function labels based on block copolymer self-assembly. Nat. Electron. 5, 433–442 (2022).
Google Scholar
Zhang, J. F. et al. Bright and stable anti-counterfeiting devices with independent stochastic processes covering multiple length scales. Nat. Commun. 16, 502 (2025).
Google Scholar
Leem, J. W. et al. Edible unclonable functions. Nat. Commun. 11, 328 (2020).
Google Scholar
Farha, F. et al. SRAM-PUF-based entities authentication scheme for resource-constrained IoT devices. IEEE Internet Things J. 8, 5904–5813 (2021).
Szaciłowski, K. Digital information processing in molecular systems. Chem. Rev. 108, 3481–3548 (2008).
Hood, L. & Galas, D. The digital code of DNA. Nature 421, 444–448 (2003).
Google Scholar
Cobb, M. 60 years ago, Francis Crick changed the logic of biology. PLOS Biol. 15, e2003243 (2017).
Lande, R. Natural-selection and random genetic drift in phenotypic evolution. Evolution 30, 314–334 (1976).
Lange, K., Zhao, H. Y. & Speed, T. P. The poisson-skip model of crossing-over. Ann. Appl. Probab. 7, 299–313 (1997).
Google Scholar
Polz, M. F., Alm, E. J. & Hanage, W. P. Horizontal gene transfer and the evolution of bacterial and archaeal population structure. Trends Genet. 29, 170–175 (2013).
Google Scholar
Feynman, R. There’s plenty of room at the bottom. In: Feynman and Computation (CRC Press, 2018).
Feynman, R. P. There’s Plenty of Room at the Bottom. In Proc. Annual meeting of the American Physical Society: California Institute of Technology (IEEE, 1959).
U.S. News and World Report, N. W. I. Machines Smarter than Men? Interview with Dr. Norbert Wiener, Noted Scientist. U.S. News & World Report, Inc. (24 February 1964).
Davis, J. Microvenus. Art. J. 55, 70–74 (1996).
Adleman, L. M. Molecular computation of solutions to combinatorial problems. Science 266, 1021–1024 (1994).
Google Scholar
Meiser, L. C. et al. Synthetic DNA applications in information technology. Nat. Commun. 13, 352 (2022).
Google Scholar
Organick, L. et al. Probing the physical limits of reliable DNA data retrieval. Nat. Commun. 11, 616 (2020).
Google Scholar
Doricchi, A. et al. Emerging approaches to DNA data storage: challenges and prospects. ACS Nano 16, 17552–17571 (2022).
Google Scholar
Ceze, L., Nivala, J. & Strauss, K. Molecular digital data storage using DNA. Nat. Rev. Genet. 20, 456–466 (2019).
Google Scholar
Organick, L. et al. Random access in large-scale DNA data storage. Nat. Biotechnol. 36, 242 (2018).
Google Scholar
Grass, R. N., Heckel, R., Puddu, M., Paunescu, D. & Stark, W. J. Robust chemical preservation of digital information on DNA in silica with error-correcting codes. Angew. Chem. Int. Ed. 54, 2552–2555 (2015).
Google Scholar
Erlich, Y. & Zielinski, D. DNA Fountain enables a robust and efficient storage architecture. Science 355, 950–954 (2017).
Google Scholar
Tabatabaei Yazdi, S., Yuan, Y., Ma, J., Zhao, H. & Milenkovic, O. A rewritable, random-access DNA-based storage system. Sci. Rep. 5, 1–10 (2015).
Farzadfard, F. & Lu, T. K. Emerging applications for DNA writers and molecular recorders. Science 361, 870–875 (2018).
Google Scholar
Meiser, L. C. et al. Reading and writing digital data in DNA. Nat. Protoc. 15, 86–101 (2020).
Google Scholar
Oliver, J. S. Computation with DNA: Matrix multiplication. In: DNA Based Computers (ASM, 1996).
Guarnieri, F., Bancroft, F. C. Use of a horizontal chain reaction for DNA-based addition. In: DNA Based Computers II (ASM, 1996).
Lipton, R. J. DNA solution of hard computational problems. Science 268, 542–545 (1995).
Google Scholar
Seelig, G., Soloveichik, D., Zhang, D. Y. & Winfree, E. Enzyme-free nucleic acid logic circuits. Science 314, 1585–1588 (2006).
Google Scholar
Stojanovic, M. N., Mitchell, T. E. & Stefanovic, D. Deoxyribozyme-based logic gates. J. Am. Chem. Soc. 124, 3555–3561 (2002).
Google Scholar
Amir, Y. et al. Universal computing by DNA origami robots in a living animal. Nat. Nanotechnol. 9, 353–357 (2014).
Google Scholar
Lv, H. et al. DNA-based programmable gate arrays for general-purpose DNA computing. Nature 622, 292–300 (2023).
Google Scholar
Adleman, L. M., Rothemund, P. W., Roweis, S. & Winfree, E. On applying molecular computation to the data encryption standard. J. Comput. Biol. 6, 53–63 (1999).
Google Scholar
Boneh, D., Dunworth, C., Lipton, R. J. Breaking DES using a molecular computer. In Proc. DIMACS Workshop on DNA Computing (AMS Publications, 1995).
Kari, L. DNA computing: arrival of biological mathematics. Math. Intell. 19, 9–22 (1997).
Google Scholar
Clelland, C. T., Risca, V. & Bancroft, C. Hiding messages in DNA microdots. Nature 399, 533–534 (1999).
Google Scholar
Cui, M. & Zhang, Y. Advancing DNA Steganography with Incorporation of Randomness, ChemBioChem 21, 2503–2511 (2020).
Meiser, L. C. et al. DNA synthesis for true random number generation. Nat. Commun. 11, 5869 (2020).
Google Scholar
Gunn, L. J., Allison, A. & Abbott, D. Allison mixtures: where random digits obey thermodynamic principles. Int. J. Mod. Phys. Conf. 33, 1460360 (2014).
Luescher, A. M., Gimpel, A. L., Stark, W. J., Heckel, R. & Grass, R. N. Chemical unclonable functions based on operable random DNA pools. Nat. Commun. 15, 2955 (2024).
Google Scholar
Luescher, A. M., Stark, W. J. & Grass, R. N. DNA-based chemical unclonable functions for cryptographic anticounterfeit tagging of pharmaceuticals. ACS Nano 18, 30774–30785 (2024).
Google Scholar
Anavy, L., Vaknin, I., Atar, O., Amit, R. & Yakhini, Z. Data storage in DNA with fewer synthesis cycles using composite DNA letters. Nat. Biotechnol. 37, 1237–1237 (2019).
Google Scholar
Wang, J. et al. Recent progress of protein-based data storage and neuromorphic devices. Adv. Intell. Syst. 3, 2000180 (2021).
Birge, R. R. Protein-based computers. Sci. Am. 272, 90–95 (1995).
Google Scholar
Ng, C. C. A. et al. Data storage using peptide sequences. Nat. Commun. 12, 4242 (2021).
Google Scholar
Yu, L. et al. Digital synthetic polymers for information storage. Chem. Soc. Rev. 52, 1529–1548 (2023).
Google Scholar
Ciliberto, S. Experiments in stochastic thermodynamics: short history and perspectives. Phys. Rev. X 7, 021051 (2017).
Collin, D. et al. Verification of the Crooks fluctuation theorem and recovery of RNA folding free energies. Nature 437, 231–234 (2005).
Google Scholar
Sagawa, T. & Ueda, M. Generalized Jarzynski equality under nonequilibrium feedback control. Phys. Rev. Lett. 104, 090602 (2010).
Google Scholar
Sagawa, T. & Ueda, M. Second law of thermodynamics with discrete quantum feedback control. Phys. Rev. Lett. 100, 080403 (2008).
Google Scholar
Chapman, E., Grewar, J. & Natusch, T. Celestial sources for random number generation. In Proc. 14th Australian Information Security Management Conference (Edith Cowan University, Western Australia, 2016).
Noll, L. C., Mende, R. G. & Sanjeev, S. Method for seeding a pseudo-random number generator with a cryptographic hash of a digitization of a chaotic system. US Patent US5732138A (1996).
Jennewein, T., Achleitner, U., Weihs, G., Weinfurter, H. & Zeilinger, A. A fast and compact quantum random number generator. Rev. Sci. Instrum. 71, 1675–1680 (2000).
Google Scholar
Figotin, A. et al. Random number generator based on the spontaneous alpha-decay. US Patent US6745217B2 (1999).
Dhanuskodi, S. N., Vijayakumar, A. & Kundu, S. A chaotic ring oscillator based random number generator. In: 2014 IEEE International Symposium on Hardware-Oriented Security and Trust (HOST) (IEEE, 2014).
Stipčević, M. Fast nondeterministic random bit generator based on weakly correlated physical events. Rev. Sci. Instrum. 75, 4442–4449 (2004).
Google Scholar
Mesaritakis, C. et al. Physical unclonable function based on a multi-mode optical waveguide. Sci. Rep. 8, 8953 (2018).
link