Over 90 malicious Android apps with 5.5M installs found on Google Play


Over 90 malicious Android apps were found installed over 5.5 million times through Google Play to deliver malware and adware, with the Anatsa banking trojan seeing a recent surge in activity.
Anatsa (aka “Teabot”) is a banking trojan that targets over 650 applications of financial institutions in Europe, the US, the UK, and Asia. It attempts to steal people’s e-banking credentials to perform fraudulent transactions.
In February 2024, Threat Fabric reported that since late last year, Anatsa had achieved at least 150,000 infections via Google Play using various decoy apps in the productivity software category.
Today, Zscaler reports that Anatsa has returned to Android’s official app store and is now distributed via two decoy applications: ‘PDF Reader & File Manager’ and ‘QR Reader & File Manager.’
Source: Zscaler
At the time of Zscaler’s analysis, the two apps had already amassed 70,000 installations, demonstrating the high risk of malicious dropper apps slipping through the cracks in Google’s review process.
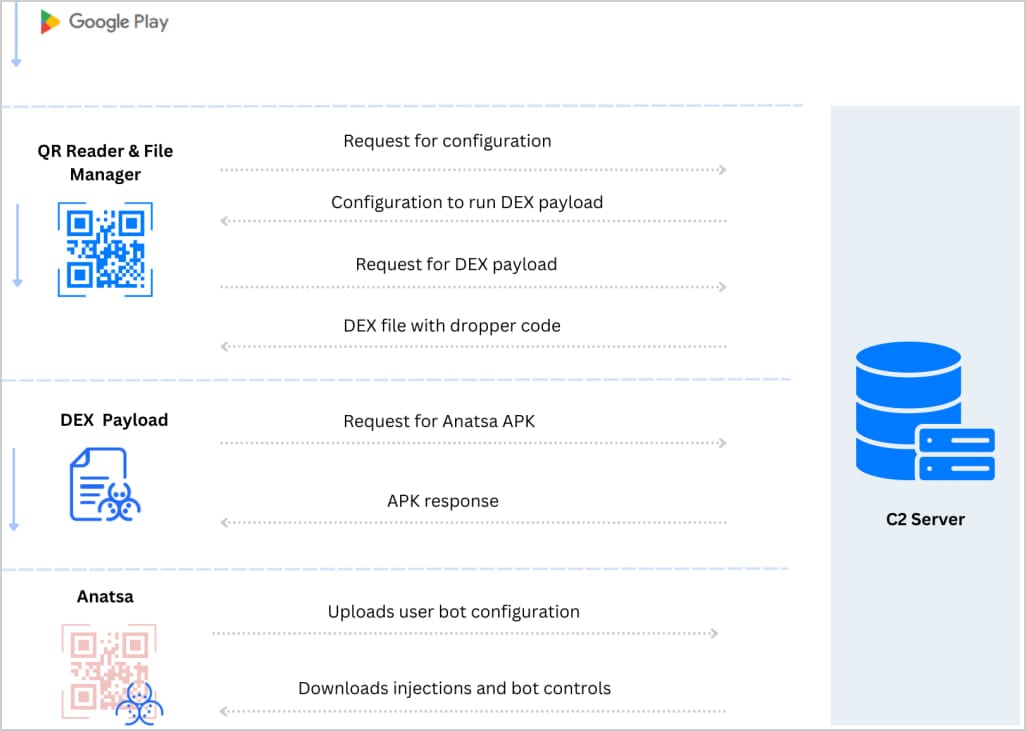
One thing that helps Anatsa dropper apps evade detection is the multi-stage payload loading mechanism that involves four distinct steps:
- Dropper app retrieves configuration and essential strings from the C2 server
- DEX file containing malicious dropper code is downloaded and activated on the device
- Configuration file with Anatsa payload URL is downloaded
- DEX file fetches and installs the malware payload (APK), completing the infection
Source: Zscaler
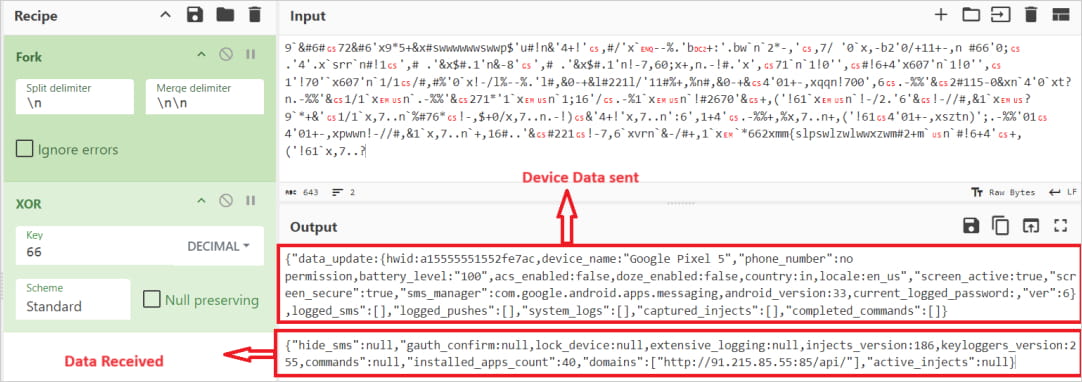
The DEX file also performs anti-analysis checks to ensure the malware won’t be executed on sandboxes or emulating environments.
Once Anatsa is up and running on the newly infected device, it uploads the bot configuration and app scan results and then downloads the injections that match the victim’s location and profile.
Source: Zscaler
Other Google Play threats
Zscaler reports that during the past couple of months, it has also discovered over 90 malicious applications on Google Play, which were collectively installed 5.5 million times.
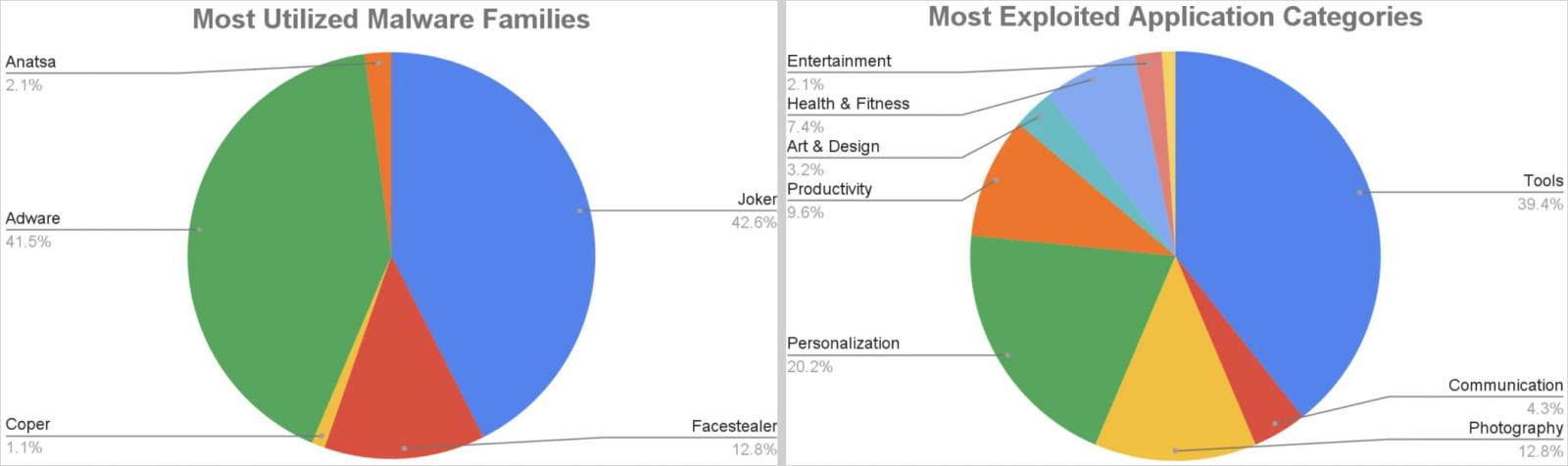
Most of the malicious apps impersonated tools, personalization apps, photography utilities, productivity, and health & fitness apps.
The five malware families dominating the scene are Joker, Facestealer, Anatsa, Coper, and various adware.
Source: Zscaler
Though Anatsa and Coper only account for 3% of the total malicious downloads from Google Play, they are far more dangerous than the others, capable of performing on-device fraud and stealing sensitive information.
When installing new apps on Google Play, review the requested permissions and decline those associated with high-risk activities such as Accessibility Service, SMS, and contacts list.
The researchers did not disclose the names of the 90+ apps and whether they had been reported to Google for takedown.
However, at the time of writing this, the two Anatsa dropper apps discovered by Zscaler have been removed from Google Play.
Update 5/30 – A Google spokesperson told BleepingComputer that the developers behind the offending apps have been banned, and shared the following statement:
All of the identified malicious apps have been removed from Google Play.
Google Play Protect also protects users by automatically removing or disabling apps known to contain this malware on Android devices with Google Play Services.
link